A recent Gallup poll found 70% of Americans aren’t engaged at work. This may be caused by boredom, low pay, lack of communication, or slow career development. Many industries are feeling the impact. They may see it in slower service, reduced attention to detail, missed sales targets, or upset customers.
But the consequences are greater when a security guard checks out. People can get hurt, businesses may be exposed to increased theft and vandalism, and stressful situations (a lost child, crowd control, or medical emergency) may get out of hand.
Around $11 billion is lost annually due to overall employee turnover according to the Bureau of National Affairs. This isn’t representative of only the security industry. That number considers more than just lost hours. It factors in the cost of finding, training, and equipping replacement workers as well as reduced productivity.
But nowhere is the issue of turnover more acute than in the manned guarding industry. High turnover rates, low retention, and employee engagement have always been a challenge for security firms and corporate security departments. Today, the high turnover rate in the security guard industry is a key challenge.
Security office and security guard turnover rates are thought to be over 100% annually. That means that the average private security firm has a completely new workforce every 12 months. It’s why it’s so necessary for security companies to do things like offer competitive wages. This can help reduce churn in a role that occasionally asks employees to risk their lives.
In addition to going over the common reasons for employee turnover, we’ll discuss wages and a few other tips in this blog that can help reduce turnover rates, increase engagement, and retain your best security officers.
-
- Increase wages and improve benefits
- Set up efficient schedules
- Ensure employees can succeed
- Offer advance and recognition opportunities
- Provide ongoing training and education
- Offer physical and mental health support
- Determine your security officers’ long-term goals
- Create a strong company culture
- Provide strong leadership
- Use software to find and retain talent
Leading Causes of Employee Turnover in The Security Industry
Let’s acknowledge the reasons behind the industry’s turnover problem before diving deeper into how to fix the problem. Here are a few:
Low pay and minimal benefits
The average hourly rate for an unarmed security officer is $15 per hour according to the U.S. Bureau of Statistics. This equates to a median annual wage of $31,470 in 2021, making living on a one-income salary difficult in most U.S. cities.
Quality security industry benefits are rare and typically limited to full-time employees. A lack of hours can knock a guard down to part-time status and potentially impact benefits eligibility.
Result: Security officers will leave for the slightest pay increase or access to better benefits.
Low employee engagement
Employee engagement is defined as the level of involvement and enthusiasm employees have for their work and workplace. An “engaged” employee will make decisions that are in the best interests of the company. They may also take the extra step for the customer.
Disengaged employees negatively affect company performance. This is through increased absenteeism, a rise in workplace accidents, and a drop in productivity or profitability. Maybe it’s a lack of recognition, training, feedback, opportunities for advancement, or a combination. Regardless, employees who don’t care are headed for the exit.
The connection between low employee engagement and high turnover rates has been well-researched. Highly engaged teams show 21% greater profitability according to Gallup. Organizations with high employee engagement outperform those with low employee engagement by 202%.
Result: Security officers will leave for another employer who makes them feel valued.
Ineffective leadership/bad corporate culture
Employees want to like their manager and perform for them. In return, they expect their manager to have their backs. However, a lack of training/mentoring, ineffective supervision, and poor communication can impact employees. They may feel isolated, underappreciated, disrespected, and ultimately become disengaged.
Result: Security officers will leave when they feel management isn’t supporting them or is being insensitive to scheduling and posting preferences.
Poor recruiting and talent management strategies
Retention starts with hiring. It takes a certain personality to be a security guard. They must be confident, aware, and compassionate. Security firms that don’t screen candidates for these qualities can expect continuous turnover problems.
These firms should also perform due diligence (background checks, personal references, drug tests, competency tests) and make applicants understand the full scope of their role.
Result: Security officers will leave after they realize they may not be the right fit for the job.
Top 10 Employee Retention Strategies for Security Officers
- There are many effects of high turnover at security firms and corporate security departments. These include:
- Increased client or organization risk because of inexperienced security personnel
- Increased recruitment and training operations costs
- The inability to provide quality service due to a lack of available workforce.
Combined, your business may be negatively impacted. Future opportunities may also be limited as a result. Physical security firms need to know how to reduce employee turnover and increase employee retention. But not to worry. We’ve got 10 actionable tips to better retain your security workforce.
1. Increase wages and improve benefits
Offering your security offers competitive wages is critical. High turnover is often the result of low wages and too few hours to make ends meet. Not sure of the going rate for quality officers in your market?
Our 2022 Physical Security Outlook eBook has average security employee hourly pay and billing rates. This data can help you benchmark your firm and attract the best talent as well as reduce turnover within your workforce.
If raising wages or offering a signing bonus isn’t possible, consider offering some type of basic group healthcare plan, or secondary benefit such as a financial wellness package. With an app like Rain, security employees can access a part of their wages before payday.
Other things to think of include supplying uniforms at no cost, giving out commuter passes, encouraging flexible schedules, or taking assignments close to home. Such perks make it difficult for an employee to leave.
2. Set up efficient schedules
Scheduling security shifts evenly can reduce overtime expenses while making sure everyone draws a paycheck. Poor scheduling and attendance practices can lead to manual work and frantic phone calls.
It may also lead to errors such as mismatched resource allocation as it relates to client requirements. This ultimately leads to increased overtime spending. Regular no-call/no-shows may be a symptom of wider employee apathy. It can also indicate a structural problem in your scheduling operations. To retain your security officers, offer them shifts that suit their lifestyle and family obligations.
3. Ensure employees can succeed
Match officers to assignments based on mutual goals, skills, and interests. Your guards will become a trusted face and part of the client’s workforce over time. It’s important that they like their post.
Do they prefer to work alone at night or with a group? Do they prefer to walk patrols, or remain seated in a guard booth or behind a corporate reception desk? Hire to fit the role.
Next, provide your officers with the tools and technology they need to effectively do their jobs. Implement a guard tour system that officers can access on mobile devices. Checkpoint tours are a smart way to keep boredom away while ensuring officers are performing their duties.
The right security workforce management solution allows officers to do things like log incidents, display messages, open report forms, capture images and video, ask questions or trigger incident alerts from anywhere on the premise.
4. Offer advance and recognition opportunities
Recognize security officer contributions by increasing their wages when possible. Spell out prerequisites and/or schedules for raises or advancement.
Reward guards after they’ve completed certification training assignments or have gone the extra mile for a client. Find security officers that stand out on your team. Think about giving them more responsibility. This can be something like a promotion to team lead. Employees who feel they’re on a career path are more likely to stay with the firm.
5. Provide ongoing training and education
Prepare your security officers for real-life scenarios by providing practical and interactive training. Make sure the training is engaging, interesting, and relevant to official duties. Consider outsourcing training. Partner with a company dedicated to providing customized online unarmed security officer training.
Know that learning doesn’t end with initial certification and licensing. After those are complete, offer continuous education, management classes, and advanced firearms training. These can all act as opportunities for career development and will help keep employees engaged.
6. Offer physical and mental health support
It’s a must to invest in security officers. Provide access to the support services they may need.
Over the past couple of years, security guards have been at the forefront of a string of both large and small crises. They’ve experienced increased aggression, verbal abuse, and threats of violence.
Security officers are also at a greater risk of experiencing gun violence simply by being on duty. It makes sense why a growing number of security officers suffer from post-traumatic stress disorder (PTSD).
Security firms must help protect their officers’ mental and physical health. This can be done by offering counseling services, medical care, or worker’s compensation after having been involved in a violent event. Such services will stand out to employees and clients.
7. Determine your security officers’ long-term goals
Few want to be frontline security guards for their whole careers. Identify the officers who aspire to be supervisors or leaders.
Make sure your officers don’t get bored with their duties. This may cause them to start looking for new opportunities. Create mutually agreed-upon paths for promotion or schedules to rotate through various management positions.
Maybe an officer wants to own their security firm one day. Take a page from Pablo Rosa Jr., who leveraged his field experience and knowledge to go from security officer to founder of the Rosa International Group. Rosa International Group provides services within the retail, hospitality, and multi-tenant property sectors.
8. Create a strong company culture
A study by EngagementMultiplier.com found 77% of employees agree a strong culture allows them to do their best work. Around 76% see the impact on their productivity and efficiency. Another 74% draw a correlation between culture and their ability to serve their customer base.
Consider these ideas when building a culture that makes your security officers feel valued and appreciated:
- Two-way communication. Company higher-ups should schedule regular status meetings with managers and supervisors. These meetings will help foster open communication and feedback. Leading by example can encourage managers to do the same with their officers.
- Team building. Actively work to stay engaged. Sponsor team-building activities such as company game nights, office parties, and karaoke sing-alongs.
- Field check-ins. Encourage managers to check in with field officers regularly. Even have officers check in on each other. This will help make sure that everyone in the company is engaged and actively contributing to the culture.
Kudos and recognition. Use a company newsletter or email blast to give shout-outs to exceptional employees. Everyone likes to be recognized. Use incentives like gift cards, and tickets to a ballgame or concert, or offer extra paid days off. Make sure everyone knows about both the kudos and rewards.
9. Provide strong leadership
Great leaders know that creating an engaging culture starts at the top. Things like employee engagement are prioritized. They’re treated as a competitive advantage and a point of differentiation.
Great leaders communicate with their managers regularly and openly. They also rely on using metrics to hire and mentor great managers. Expectations of guards are widely communicated.
Strong leaders develop and stick to strategic business plans. These set the company tone and direction which can improve employee retention.
10. Use software to find and retain talent
The security industry is notorious for high turnover and makes recruitment continuous. It’s been difficult as a security manager to walk the line between tight margins and retaining your best resources. But today’s technology makes it easier to create an environment that favors retention.
Human resources (HR) recruitment software can help security firms find the best talent, by:
- Streamlining administrative tasks
- Speeding up the application process
- Scoring candidates
- Retaining seasonal employee data for callbacks
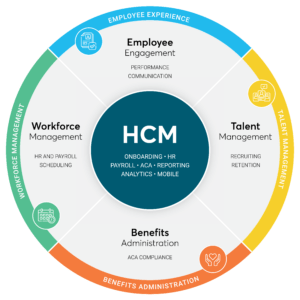
The best HR recruitment software works well with payroll and scheduling applications post-hire. Sometimes HR recruitment software is part of a larger solution suite referred to as Human Capital Management (HCM).
No matter the name, recruitment software helps find stronger candidates. Great recruitment software publishes links to job postings on popular websites, provides scheduling, helps conduct video interviews, sends offer letters, and helps with compliance reporting.
Time and labor management solutions like TrackTik’s HCM software use actual scheduling data to run accurate and regular payroll. This helps reinforce the firm as a responsible and reliable employer. Managers can limit overtime expenses while keeping more officers happy with tools to distribute staff shifts.
Plus, tracking and analyzing operational data can help supervisors recognize and reward high-performing individuals. Managers can consider ways to incentivize officers as appropriate.
Reduce Guard Turnover While Increasing Retention and Profitability with TrackTik
Physical security industry recruitment and retention are ongoing and require constant attention and improvement. Knowing how to reduce employee turnover must remain a priority for private security firms. But it’s worth the effort, especially when knowing that the average cost of replacing an employee is 25% of their total salary.
Understanding the causes of officer turnover is step one. Implementing our suggested hiring and employee retention strategies is step two. Step three is knowing whether you’ve got the right solution to support your operations.
We’ve made it easy and have laid out all the information you need to consider in our guide, Why (and how) To Switch to a New HR & Payroll Platform.





 Why is Lone Worker Safety Important?
Why is Lone Worker Safety Important? Protect Your Lone Workers with TrackTik’s Guarding Suite
Protect Your Lone Workers with TrackTik’s Guarding Suite