Threat detection and investigation is at the core of any security operations. It’s the reason security exists in the first place. And yet, many security operations still use strictly manual processes for threat detection. Most operations have CCTV cameras for manual viewing, but these only allow for reactive responses to threats. There are more options out there that enable security to take on a proactive approach to threat.
Limitations of CCTV cameras for security operations
One of the staples of threat detection is the CCTV camera. The prevailing wisdom has been that with a camera giving you a visual on vulnerable points on a site, you can see threats in real time. To manually monitor all these cameras all the time is impossible or would cost more than any organization is willing to spend on security. It’s estimated, among security professionals, that over 90% of security video goes unseen and is usually only watched after an incident. The obvious result of this strictly manual surveillance is that security misses threat signals.
Facial recognition software is being implemented into CCTV camera systems, but the technology is still limited. Facial recognition tech struggles with lighting conditions and masked faces, which are common occurrences during incidents of theft. There are also privacy concerns, as individuals are being subjected to surveillance and identification without giving any form of consent.
Use of these cameras alone also fails to give insight into where security operations are most vulnerable or how to make strategic changes to the use of resources. Security is still reactive in this manual mode, and not proactively preventing future threats.
Data and analytics for going beyond reactive security
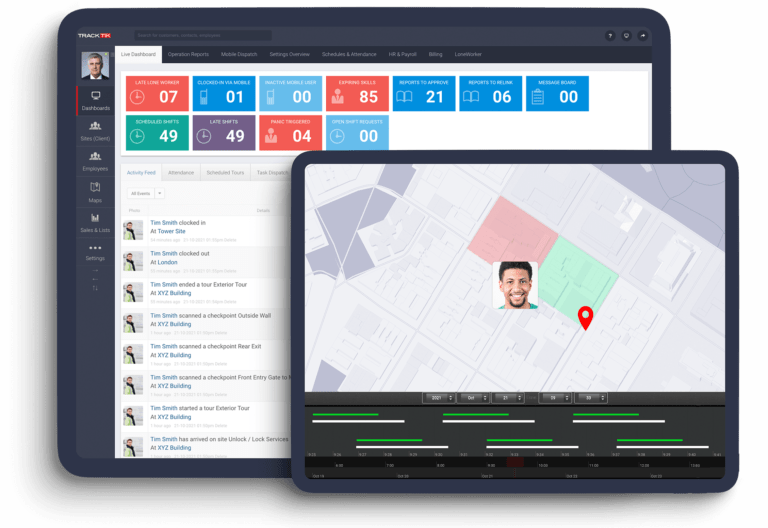
Only by using data and analytics can security operations make the leap from reactive to proactive threat prevention. Having real-time and historical data allows a security manager to derive actionable insights about their operations, leading to concrete threat prevention.
Provided the data in question contains the right amount of detail, productive changes to strategy are possible. For example, if incidents frequently occur in a specific location, and the incident data logs the location, time and type, the security manager can look at that data and make sure there is a stronger guard presence there or more frequent tours cover that location.
How to get data out of your physical security operations
Incident reporting is an obvious area of security operations that can be used to collect data from, but the reality is that you can capture data from your entire operations provided you have the necessary software.
Incident reporting
Technically, you can get data out of your manual processes. All you have to do is make sure your guards are writing down detailed incident reports; those reports are collected and organized; then put into an excel spreadsheet, then turned into analytics. While it’s certainly possible, it’s a lot of work compared to having these processes automated with software that features incident reporting along with data and analytics.
Patrol

Incident reporting isn’t the only way to generate useful data. Provided patrol cars are tracked and times logged, the data generated here can be used to optimize patrol routes. If guards are always failing to arrive at a specific patrol site on time, the data can give you insight into why that’s the case and help you plan a better patrol route to correct this tardiness.
Scheduling
With scheduling software that captures data, you can keep track of which guards are failing to cover their shifts, jeopardizing the safety and security of a site as a result.
In a survey where security leaders selected their top three areas of investments, 83% chose big data and analytics, making it their highest priority. It won’t be long before big data and analytics are not just a plus for security but the standard that all stakeholders come to expect.
CCTV will help with coverage in the field but without robust data and analytics, security operations are limited to being reactive to threats. To run a proactive security operation, detailed data needs to come in from both the field and back office, informing strategic decisions and staffing. Not only will security be better equipped for threats, but there will be plenty of evidence in the data and analytics to demonstrate the true value of security operations.
How do you use data in your security operations?